Hi again! I hope you're keeping safe and healthy.
Previously, I've hinted at a big, unannounced feature of Prometheus Wept. Finally, enough progress has been made to talk about it. To begin, you may be aware that Prometheus Wept takes place in the aftermath of a cyber attack which corrupted most of our digital technology.
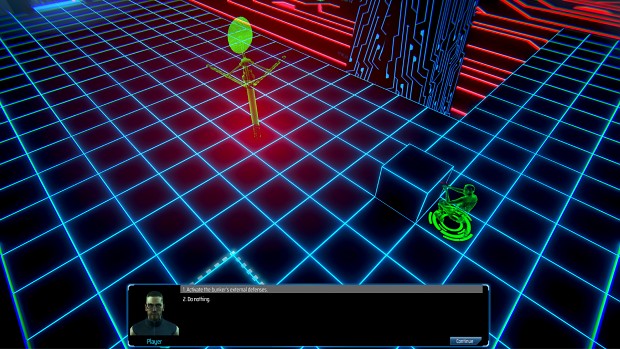
The new feature allows the protagonist to digitise their consciousness and enter corrupted computer networks as an avatar. This means that two turn-based battles can occur simultaneously and the actions taken in one battle can affect the other. Typically, this will involve your allies protecting the player character from physical enemies, while your avatar battles the network's security protocols.
Each network is comprised of a number of nodes. Each node controls a system in the physical world, for example a door or defences. When an avatar defeats and captures a node, the player gains control of that system. To make more sense of this, here's a concrete example which will be available in the upcoming demo.
You can find more info and add Prometheus Wept to your wishlist on Steam!
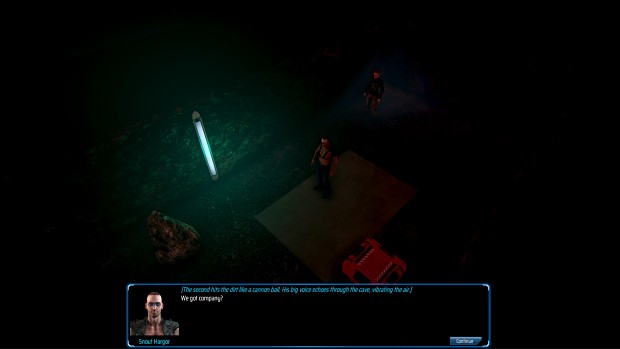
In the company of your first companion, Ferdia Galloway, you discover an underground complex.
You continue along the tunnel until you are accosted by the complex's mysterious guardian.
There's no way you're getting through the door, but there is a terminal nearby. You might be able infiltrate the network and get control of the door that way, however, when in cyberspace, you can't act in the physical world.
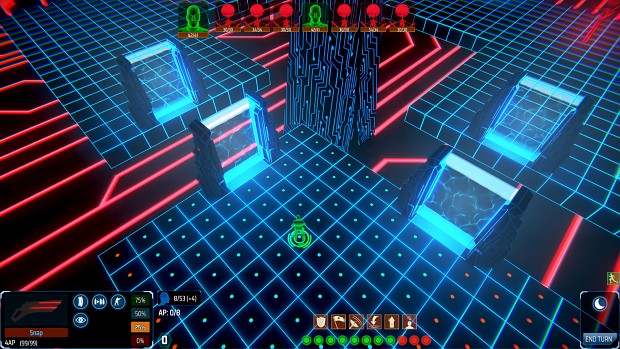
Here we are. Cyberspace. The terrain is fragmented, but you can use the portals to island hop. You can use viral projection, a ranged attack, on any hostiles. At the bottom centre of the screen there are six buttons, which correspond to abilities called scripts. Scripts cost power to run and you generate power each turn in cyberspace based on your tech stat.
Using the ScanNode() script, you discover that Node B is responsible for external defences. The other two nodes control the main door and interior defences. Node B is a good place to start, in case you are attacked in the physical world. Spoiler: you will be.
The node's attack range is greater than yours, but you manage to avoid its attacks. You don't have enough AP to close in and make an attack this turn, so you call the SetMemoryLocation() script, which allows you to relocate to a position up to five tiles away.
You've got one last trick up your sleeve. You call the InstantiateCover() script to create cover to help protect from the nodes attacks.
Control returns to the physical world. All quiet... so far.
You've beaten the node and used CaptureNode() on it. You switch on the external defenses. The node will now attack any enemies in range and provide you with power every turn. Even with the cover, your avatar has taken a lot of damage. You use Avatar.Debug() to repair some of the damage and head towards the next node.
And back to the physical world, where trouble, in the form of a group of marauders, has just found you. Thankfully, it's going to take them a few turns to reach you.
The entrance turret is online and two retractable cover plates have extended to offer protection to Ferdia, who readies his weapons, a pipe pistol and a more powerful, single shot pipe rifle. Each ally has a unique set of abilities, so Ferdia has a couple of tricks up his sleeve too, but we'll get to that another time. On the next turn in cyberspace, the avatar can exit, but the player will lose a turn due to transfer syndrome, an ailment caused by the jarring effects of returning to the physical world.
There are multiple ways to handle this encounter: exit cyberspace immediately and fight, try to activate the exterior defences before the marauders reach you, or open the door and try to use the hostile-to-all internal turrets to your advantage.
The intention is to allow players to upgrade and create scripts using the computer science skill and to customise their script selection within the limits of the RAM on their data warfare suite. I'll follow up in the not too distant future with a video of this encounter and some more screenshots of in-game locations.
If you have any feedback or questions, it would be great to hear from you!
Take care,
Daithi