Functions:
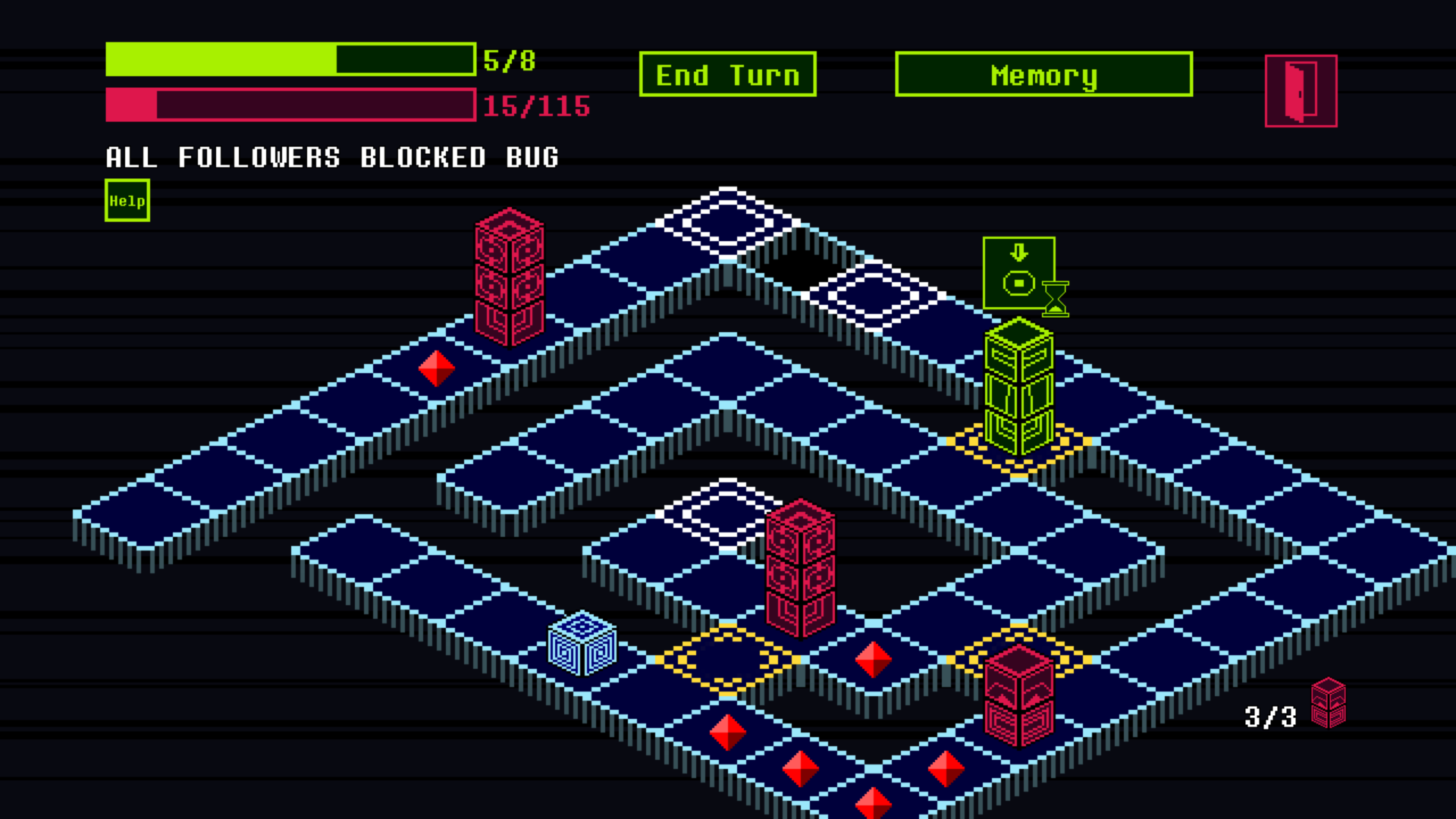
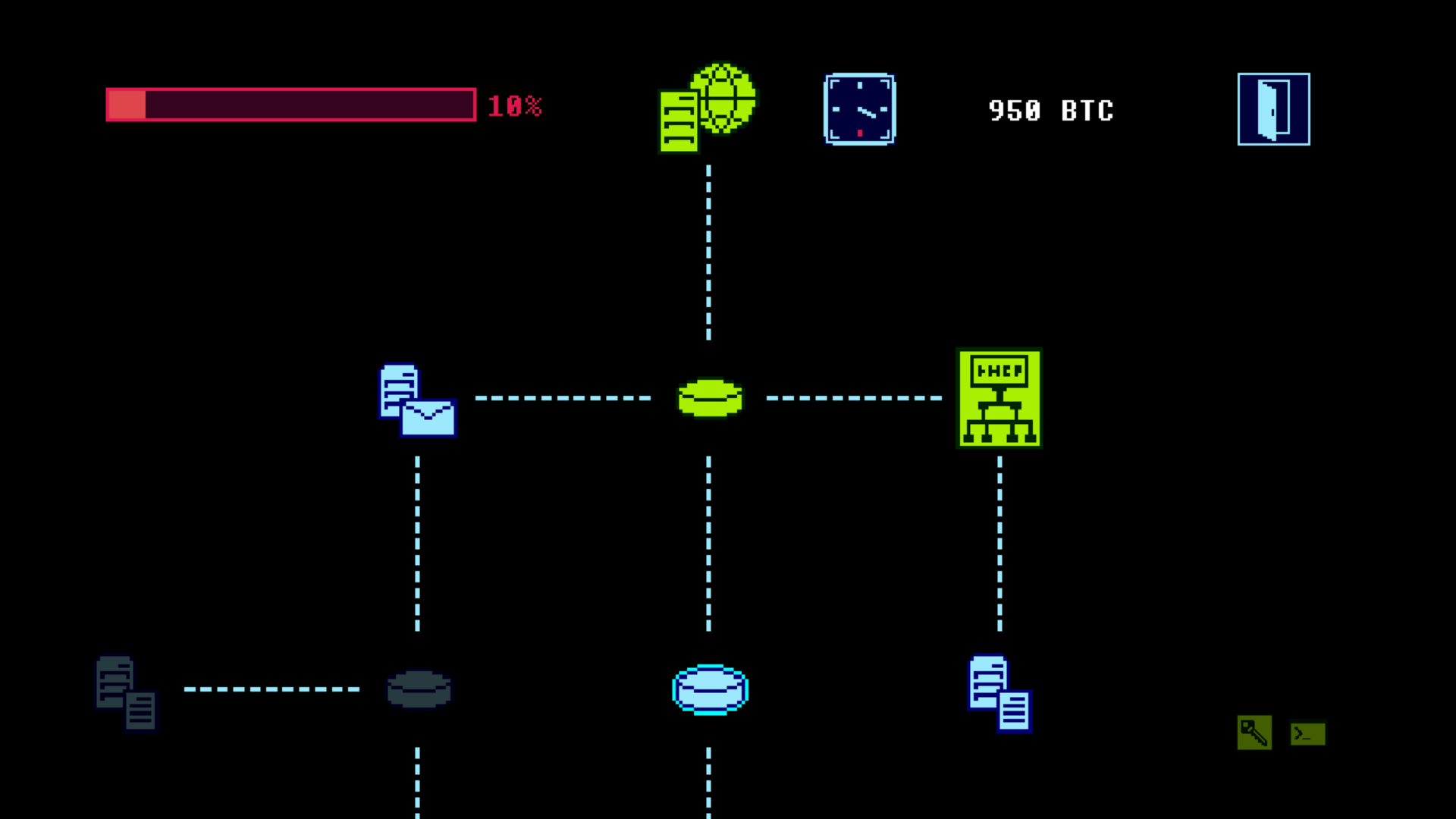
At the beginning of each level (server) you control only one unit (malware), that can only move. To acquire new skills you have to download Functions from specific tiles within the level.
The Copy function for example allows a malware to create a copy of itself; the Jump function marks a tile so that a malware can teleport over it. Each function occupies memory slots.
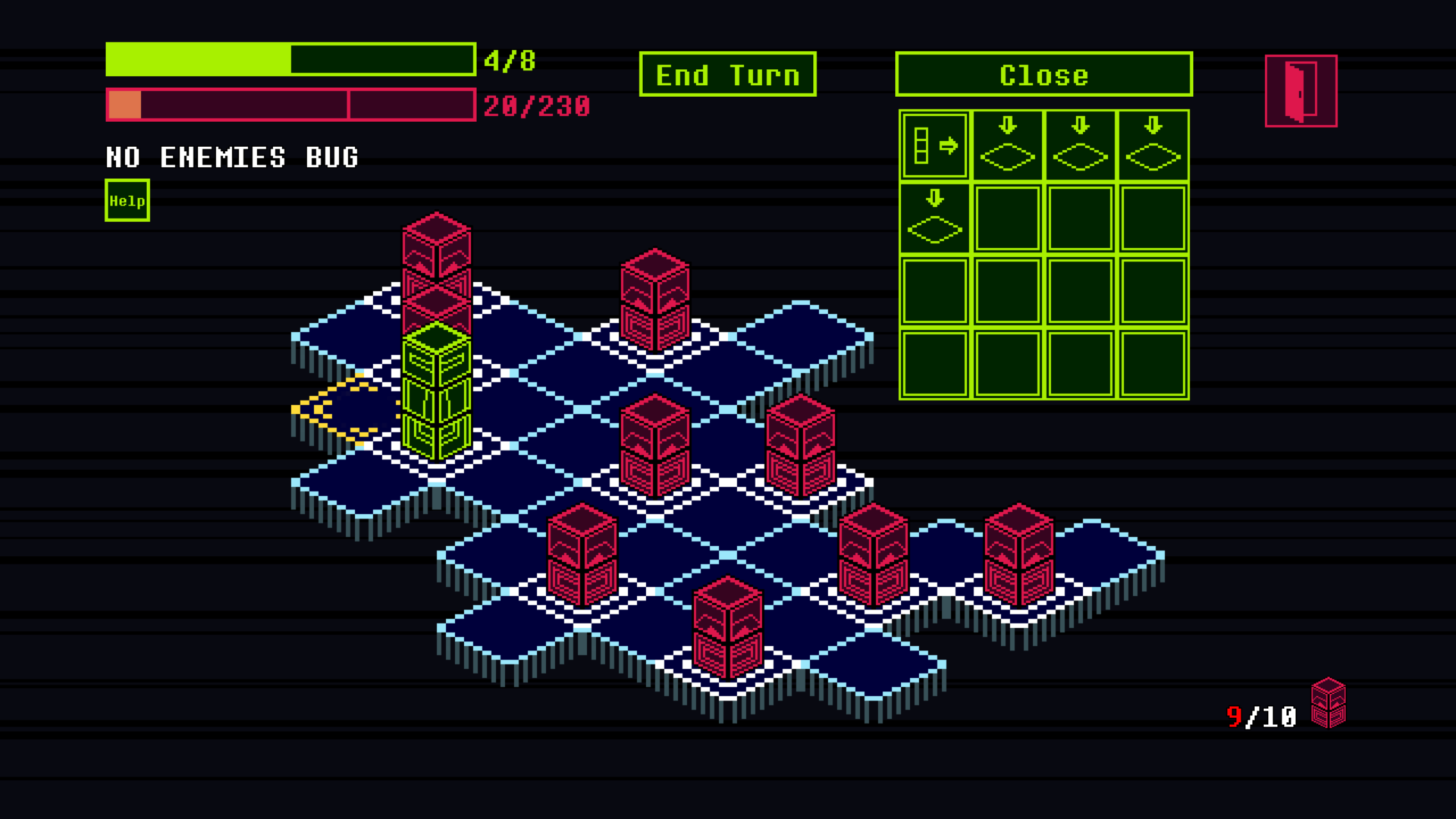
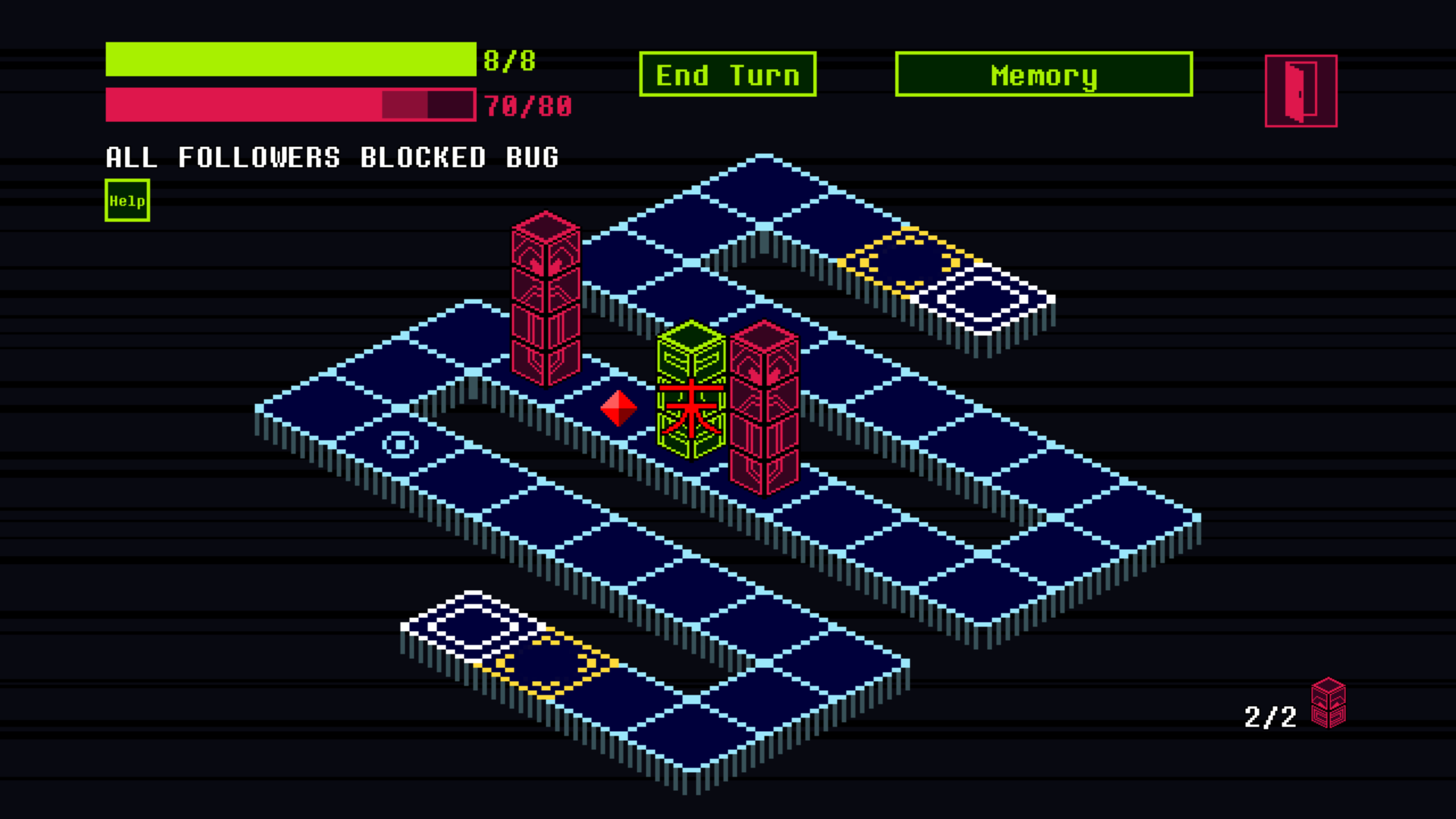
Bugs:
Functions are needed to achieve each level's goal: trigger the level's bug and make it crash.
For example, the Spawn Bug occurs when the server has to spawn a new enemy and all the spawn points are occupied.
Enemies:
Each turn you plan your moves by analyzing what enemies will do in their next turn. Enemies have simple and predetermined behaviors. They can be destroyed by crossing them as in checkers.
If a malware is hit by an enemy it loses its last downloaded function and if it has no more functions it is destroyed.
Alarm Level:
One of the fundamental goals of a hacker is to leave no trace. Some actions will increase the server's alarm level. For example when you destroy an enemy or download a function. If the alarm level reaches its maximum value the intrusion attempt fails.
Networks:
Levels are arranged in networks. Your ultimate goal is to reach the database server and hack it. Depending on the type of hacked server you can get different bonuses (i.e. File Servers allow you to earn bitcoins, DHCP Servers to get the network map).
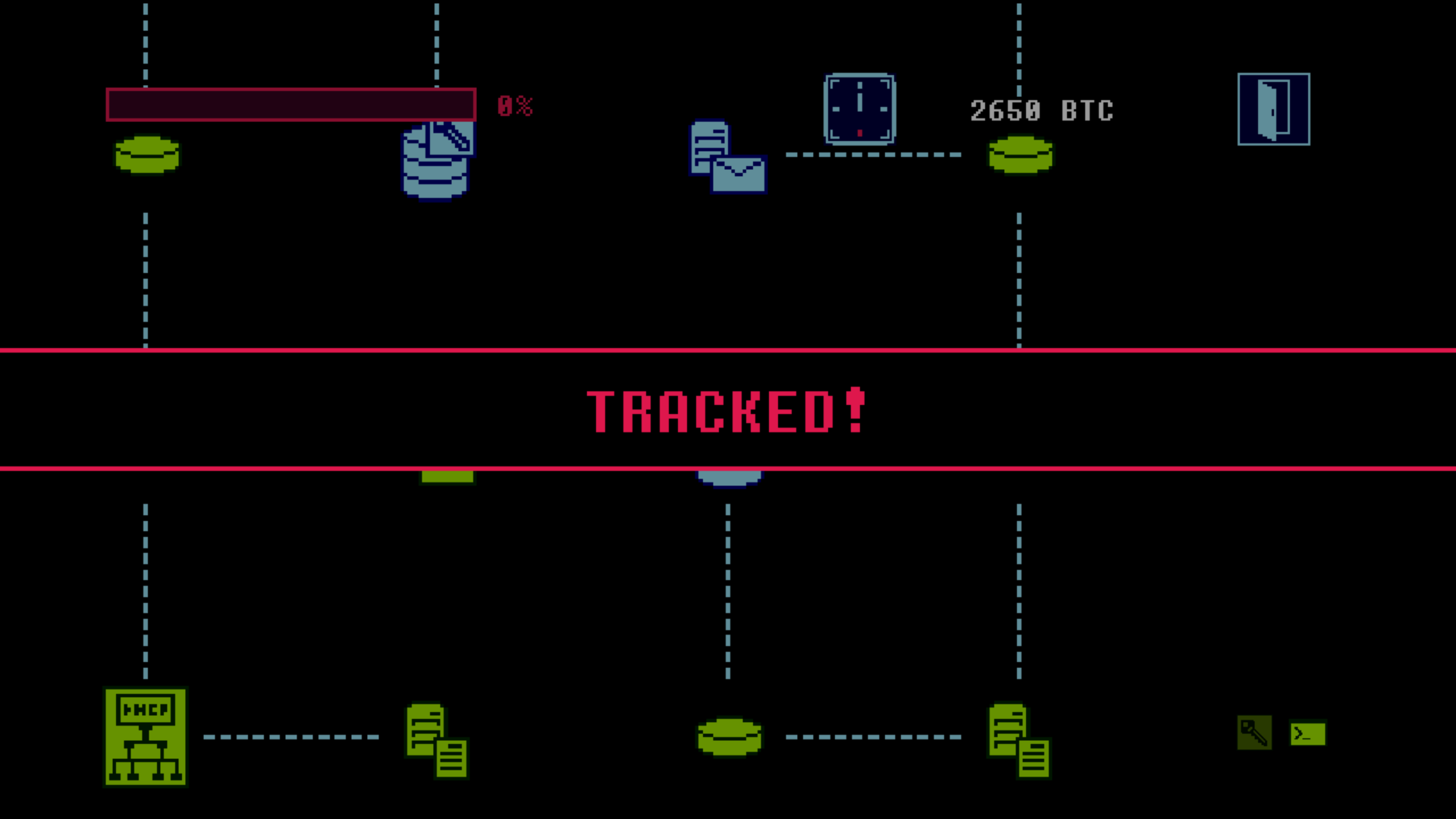
Each network must be hacked within a certain number of nights and each night you have up to six intrusion attempts. When you fail to hack a server the tracking level goes up and when it reaches 100% you are arrested.
The following video shows you some of these concepts in action (in particular how to exploit the spawn bug).
If you're interested follow the game on Itch.io or GameJolt.


Looks super cool! Love the graphics style. And very creative job with the gameplay, sort of stealth puzzle mechanics.
thanks a lot!