Cheating and hacking is a rather large issue in multiplayer games, particularly in the FPS genre. Common hacks that can ruin gameplay for other players include flyhacks, speedhacks, aimbots, and wallhacks.
In order to discourage hacking, War of the Voxels takes a "multiple lines of defense" method of preventing cheating. There are three lines of defense:
- Frequent weekly code obfuscation
- A strong authoritative server
- Heuristic analysis of a player's actions
Frequent weekly code obfuscation
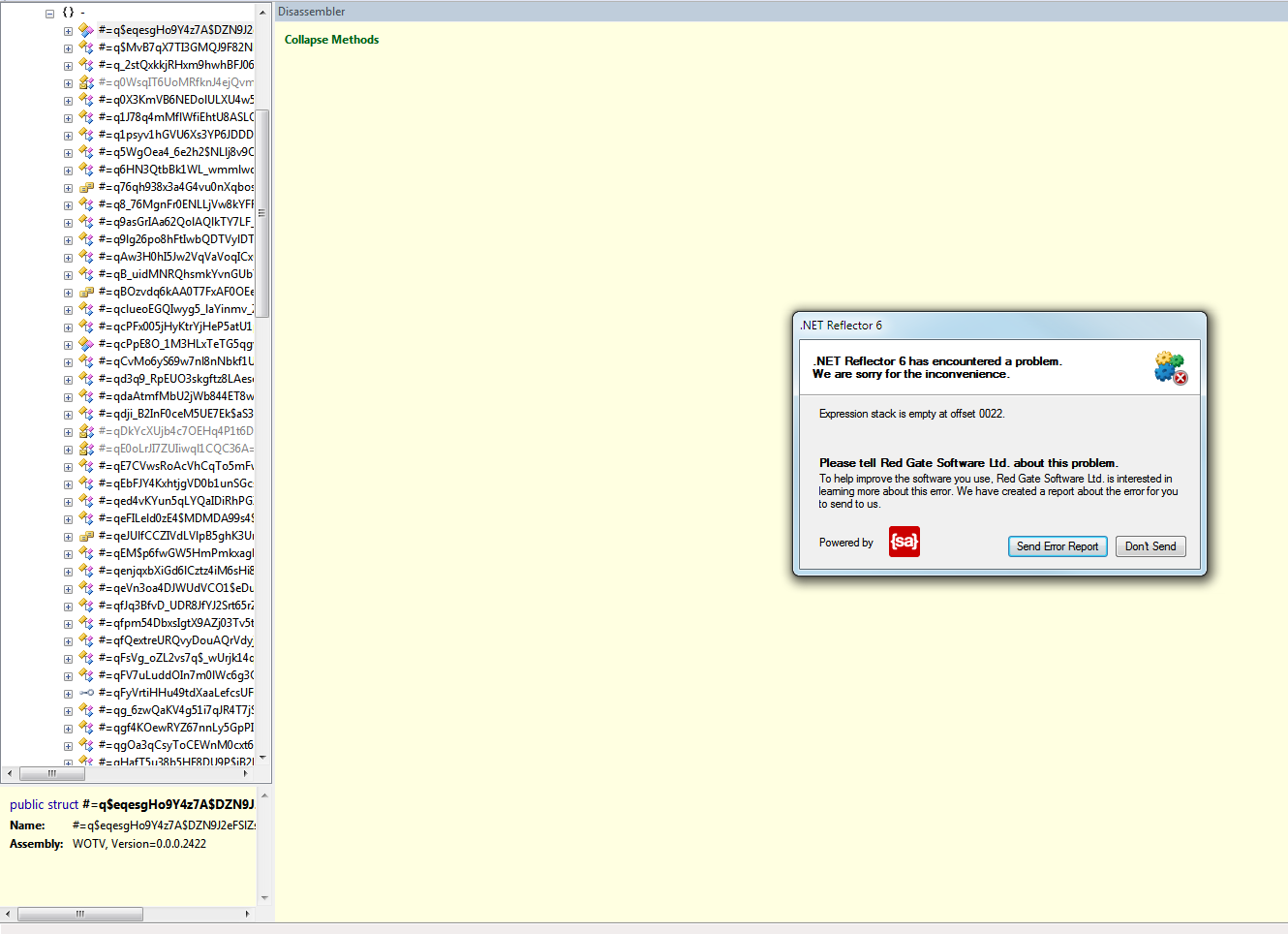
War of the Voxels is especially vulnerable to hacks, as it is written in C#, a language which can easily be decompiled. Most C# applications can easily be decompiled and recompiled with changes. However, War of the Voxels is obfuscated; when decompiled, instead of seeing the original variable and method names and control flow, a decompiler would see:
This obfuscation of the code primarily accomplishes three tasks:
- Discourages would-be hackers from modifying the source code.
- Delays the development of most hacks. Modifying the code without deobfuscating it in some way could prove to be difficult.
- Makes developing hacks more difficult, as progress would need to be reset after a new obfuscation.
Of course, this line of defense only works as long as someone is maintaining the weekly updates, and therefore is not a good option for final versions.
A strong authoritative server
To combat any cheats and hacks that make it past the obfuscation layer, we've tightly integrated security into the networking code. Our networking has been designed specifically with three goals in mind:
- To create a fair and fun playing environment.
- To not detract from the gameplay experience to prevent cheating.
- To be fast and reliable.
What does this mean? Put simply, we want to disable most hacks without sacrificing the gameplay experience. One major category of hacks that this line of defense prevents is movement hacks. All movement code is authoritative. When a player presses the "move forward" key, the client sends a request to the server to move forward. To mitigate the effects of lag, the client simulates both other players and the current players locally. When the server receives the input messages, it processes them and determines the master authoritative position. This is then sent out to all the clients, which correct their predicted positions to the server's authoritative position.
So what does this mean?
Well, since input is handled on the server and is merely simulated on the client, a client who attempts to "flyhack" or "speedhack" by modifying their position is only fooling themselves.
Heuristic analysis of a player's actions
Finally, we apply some heuristic analysis on player actions to determine if an action was legitimate. For example, a server may collect information on a player's kills over a match. If the server recognizes that, for example, Player A has been killing with headshots for a large portion of their kills, the server may temporarily disable one-shot kills and see if the player's performance worsens. The server may also check how fast a player turned to shoot someone. If the victim was out of a player's field of view, and the player turned around 180° in less than 100 milliseconds, the server might flag the action and make the player's shots shoot inaccurately or deal less damage.
Putting it all together
The result of these three lines of defense is an extremely flexible and secure online gaming experience. With hacks either completely defeated or disabled to the point that a human could defeat them, hacks can quickly become obsolete and "useless".




Sounds absolutely wonderful!
Keep up the good work.
This anti-hax method is really innovative and unique! I don't know why game developer haven't think of it.
These methods are actually the baseline of anti-hack protection employed by any self-respecting online game developer.
I'm not fond of the heuristics based approach, as I think without a true divergent way of assessing the data gathered, you stand a strong chance of hindering legitimate players. That is not fun, fair, nor balanced. It just makes a mess of non-equivalency and ups and downs. In many cases, I can even see it punishing a good round for someone. Punishment is something inherently to be avoided in game development.
I can see a heuristics based approach being quite useful, but certainly not in the proposed form.
I have seen this happen in other games before, some people are just very skilled at gaming. Being banned for getting head shots or playing for extended periods of time does not make you a cheater.
But there are limits to human responsiveness, and to humans are prone to make mistakes.
If a player has made nothing but head shots for 30 days straight, or has not stopped playing for over 30 days changes are something is wrong.
(1) Creating "patches" for hacks isn't my area of expertise, but if their is anything I have learned over my short years, from others, when it comes to security, in just about anything.
Their is no point in telling people what they don't need to know. All it does is tell them what to look for and ignore and saves them weeks of hair pulling because you tell them pretty much to what you are doing.
(2) Great idea or not, history is littered with genuinely good ideas that end up in flames. I don't know if it will work. But please don't get conceited over this small victory.
The way I see it, there's no way of "hiding" these protection methods from the players. All of the methods I have listed are quite extensively used in multiplayer games. Obfuscation would instantly be noticed when a potential hacker tries to decompile the code, the authoritative server model could easily be discovered through sniffing packets or messing around with lag, and the heuristics part would be discovered after some hacker successfully understands the decompiled server code.
Sounds like you guys are putting some solid work into anti-cheat measures. Which is a great idea.
But a lot of what you are doing seems to by at the high level of the development lifecycle.
I personally don't see how these measures are going to stop someone opening OllyDBG, and dissembling the code into ASM. Or reading the raw memory values straight out of memory.
Heuristic is a solid idea, measuring players against players to pick out anomalies is definitely going to pick out a few of the more stupid cheaters. But again I don't think this will prevent wide spread use.
I would be very interested in hearing your feedback. The purpose of this message is not to condemn what you are doing. I an fact, I think it will have an impact. I would just like to learn more.
Also one last thing, a lot of the people who write these cheats do it for fun, for a challenge. You may have just inadvertently challenged someone to best you :-D.
Sure, you can easily read memory from the game. The question is: what are you going to do with that data?
The information could be mouse position, enemy player position, health.
All of these things are useful, change the value and call any internal function that reads/writes that memory location and you have a simple bot that does head shots, or an auto heal bot that spams health potions when you are low on health.
The point I am trying to make here is obfuscating code will not stop botters, as most Debuggers or Memory scanners these days will find a list of functions that read/write to a memory location for you. Hell when you get down to the raw ASM its all about offsets and labels, function names are not important.
You're assuming that the client will receive the information in the first place. What business does a player have knowing the health of another player or the position of another player if the other player can't be seen?
You also say that you could automate functions to spam, for example, health potions. I could easily add a cool down time between item usages, which would instantly make the automation useless.
Is the described method foolproof?
No, but it sure will cripple most hacks to the point of almost being useless.
I am afraid I disagree. Any information the botter has access to is an advantage, and any information the player can see on his screen or that is passed to the client (a players own health, or the position of an enemy) the botter will also have access to.
The automation of any task will also give the botter an advantage, if you take into account the average players connection latency + human response time this is considerable slower than a bot. To make matter worse a bot only has to beat this value by less than 100ms (very hard to detect), then he will win every time.
But please do not get the wrong idea, I applaud your effort, no anti cheat measure if fool proof. You guys are trying to make it harder which is a solid start.
A few helpful tips that you could implement are:
1. XOR any value that is shown to the player on screen
2. In your weekly code patches, add semantically null code in to important functions.
These will not stop a determined person, but it will slow him down.
Nice post! I would recommend including also another powerful hack prevention. Kill cam and vote kicking. It's hard so much harder to fool a human than a computer algorithm.
Do you have any ideas on how to prevent graphical hacks like looking through walls?
/Johan
Kill cams are helpful, and you are right on the money computers are very dumb. Its much harder to fool a human.
Wall hacks from what I have seen in the past are possible because game developers send to much information to the client. Information about what is happening in areas that the player is not current in or can not see.
But this is a two fold issue, because they may be heading in that direction, and if the information doesn't get there in time the game looks buggy. Also the information might be needed for sound effects, things the player can hear but not see yet. For example behind a door.
As someone who frequently decompiles C# code, I can tell you that this sort of obfuscation is so easily removed, it might as well not be there. Effective obfuscator creates IL code that can NOT be represented as valid C#; and preferably code that crashes popular decompilers outright.
I made the mistake of uploading a picture a couple months old.We now have CFO, and attempts to view the code will crash some decompilers (namely Reflector).
As for ease of deobfuscation, that is only intended as a minor "setback" for a would-be hacker. The main issue would be understanding what does what. The rest of the defenses are for the intermediate-to-advanced that get through.